A Deep Dive into Sidechains and Layer 2 Solutions for Improved Performance
There are three desirable properties that blockchains try to achieve: security, decentralization, and scalability. A well-known trilemma in the blockchain realm stipulates that only two of these properties can be achieved simultaneously within the same system, with a compromise on the third. In Ethereum, security and decentralization are prioritized over scalability.
As the number of people using Ethereum grows, a bottleneck of transactions is created: transaction speed slows down and gas prices rise. This cycle impedes Ethereum’s adoption at scale. Simply increasing the number of transactions per block would compromise decentralization, because it would become more expensive for people to run Ethereum nodes (independent copies of the Ethereum transaction history). Additionally, very large block sizes could destabilize consensus, compromising security. To address these challenges, various categories of scaling solutions have emerged, like sidechains and Layer 2 solutions.
Sidechains
A sidechain is a distinct blockchain that operates alongside the Ethereum Mainnet, which optimizes its consensus algorithm and block parameters for greater throughput. However, since a sidechain is essentially just another blockchain, a sidechain’s increased scalability comes at the cost of security and decentralization (the scalability trilemma).
In contrast to Layer 2 (L2) solutions, sidechains do not publish state changes or transaction data on Ethereum, and they do not inherit Ethereum’s security. Additionally, sidechains require higher trust assumptions and do not achieve the goal of trustless security, making them more vulnerable to attacks. They are susceptible to issues like chain reorgs.
Layer 2s
Off-chain solutions that rely on Ethereum for consensus and security fall under the category of Layer 2 solutions. These solutions are designed to help scale your application by processing transactions off the Ethereum Mainnet (Layer 1), while still benefiting from its decentralized security model. A Layer 2 is a separate blockchain that extends Ethereum and inherits the security guarantees of Ethereum.
Transactions are submitted to the L2 nodes instead of L1, and then ultimately settled back on L1. Once submitted, the transactions are secured by Ethereum L1 and cannot be altered. The details of how this is done vary between different L2 solutions.
State Channels
A state channel is a communication environment between the transacting participants.
A State channel is a protocol where users can transact “x” number of times with one another ‘off-chain,’ while only submitting two on-chain transactions to the Ethereum Mainnet. The channel uses cryptography to demonstrate that the final data generated is truly the result of a valid set of intermediate transactions.
Each channel is managed by a smart contract. To open a channel, participants deploy the contract and deposit funds. To start transacting off-chain, both parties sign a state update. To close the channel, participants submit the last agreed-upon state on-chain, and the smart contract distributes funds according to each participant’s balance in the final state.
State channels offer advantages such as higher throughput, increased privacy, reduced latency, and lower costs compared to on-chain transactions. They can be useful for microtransactions, decentralized applications, and conditional payments according to the state machine’s final states.
State channels have a couple of drawbacks, such as the assumption that all participants will be online to monitor and respond to disputes, even invalid ones, or risk losing their funds. The number of participants that comprise a state channel remains fixed throughout its lifetime, limiting its usefulness.
Compared to rollups, state channels offer lower security since they do not publish all transaction data or state commitments to the mainnet. However, their connectedness to the Mainnet exceeds that of sidechains, making them relatively safer.
Rollups
A rollup is a type of L2 solution that moves transaction computations off-chain while storing transaction data on the Mainnet. This allows rollups to inherit Ethereum’s native security, which relies on Ethereum’s decentralization.
Here is how a rollup works: thousands of transactions are being gathered into a batch. All transactions in the batch are processed off-chain. The information from these transactions is then bundled into one transaction and is sent to be submitted on-chain.
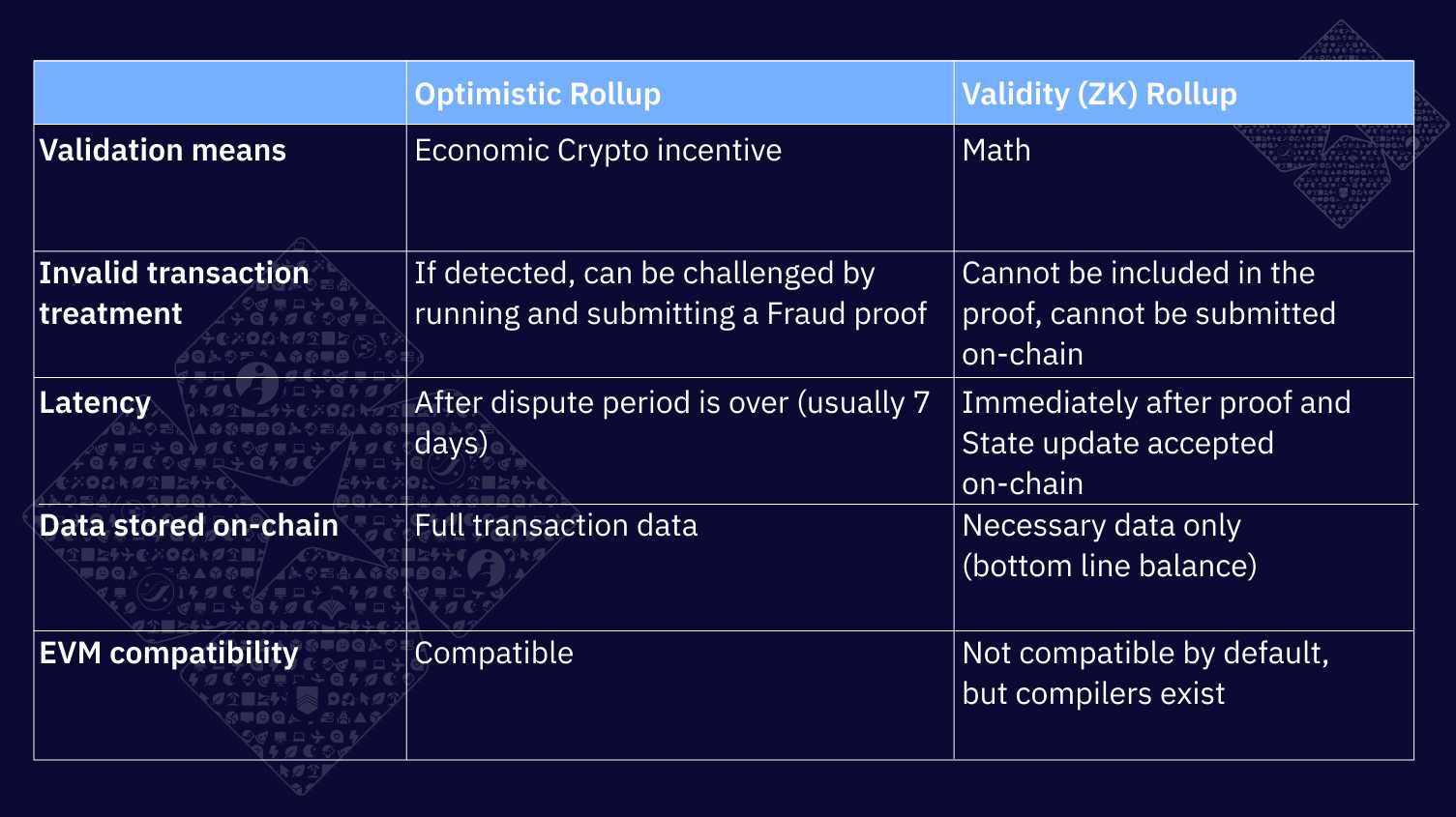
Based on the method of rolling the computations off-chain, we get two types of rollups: Optimistic and Validity rollups.
Optimistic Rollups
Optimistic rollups operate under the assumption that all transactions in a batch are valid and do not perform any computation by default. If a transaction is deemed invalid, there is a challenge period during which anyone can challenge the transaction by generating a fraud proof. Successful fraud proofs trigger a re-execution of the disputed transaction and update the rollup’s state accordingly. Optimistic rollups are EVM-compatible and can use native Ethereum tools to build on top of them.
Validity Rollups
Validity rollups, also known as zero-knowledge rollups, bundle transactions into batches and process them off-chain. Then, the off-chain prover creates a validity proof for the validity of the transactions in the batch. Validity proofs are cryptographic assurances that the state change proposed by the rollup is the result of executing a certain batch of transactions. Rollup operators then post a summary of the changes describing all the transactions in the batch, along with the validity proof.
Validity rollups use mathematical proofs to automatically ensure the integrity of transactions and secure the protocol. Validity rollups are not EVM-compatible by default, although compilers for validity rollups on Starknet exist.
Although rollups are still under development and may not be as secure as Ethereum in some aspects, they have already shown promising results in projects like StarkEx.
StarkWare’s validity rollup solution StarkEx has already processed 392M transactions and has 907Bn USD cumulative trading volume across all its applications ranging from DeFi to NFTs.
Summary
An increase in Ethereum users creates a bottleneck of transactions, slowing down transaction speeds and raising gas prices. To address these challenges, various categories of scaling solutions have emerged, like Sidechains and Layer 2s.
Sidechains and L2s both take a similar approach to scaling, by moving the transaction execution off-chain. But sidechains are responsible for their own security, while L2s inherit Ethereum’s security, allowing L2s to scale without compromising decentralization and security.
Rollups are a Layer 2 solution that moves transaction computations off-chain while storing transaction data on the mainnet, which allows them to inherit Ethereum’s native security. There are two types of rollups: Optimistic and Validity rollups.
Validity rollups have an edge over optimistic rollups in that they prioritize the security and integrity of transactions by requiring every transaction to be verified on-chain. This ensures that all transactions are valid and prevents any fraudulent activity from occurring. On the other hand, optimistic rollups rely on fraud proofs to detect invalid transactions, which can lead to delays and potential security vulnerabilities.
Starknet is a validity rollup that uses STARKs instead of SNARKs, which makes it secure against quantum computers and eliminates the need for a trusted setup. Want to scale your dApp using STARKs without needing to understand the underlying tech? Learn Cairo to build on Starknet today!